Control what AI coding agents can
see, touch, and do
Unbound is the world's first Agent Access Security Broker (AASB) to govern the security, compliance, and policy of your AI coding agents.
Trusted by security-forward teams






What can AI coding agents do?
Every developer now has an autonomous AI agent with terminal access, MCP connections, and full developer credentials. Security teams have zero visibility.
Terminal Access
Agents run shell commands — rm -rf, git push --force, database queries — with full developer permissions.
MCP Connectivity
Unsanctioned MCP servers extend agent reach into Slack, databases, cloud APIs, and internal tools.
Data Exposure
Secrets, PII, and internal source code flow to unvetted models and third-party MCP servers.
Inherited Permissions
Agents inherit the developer's full credentials — SSH keys, API tokens, cloud IAM roles.
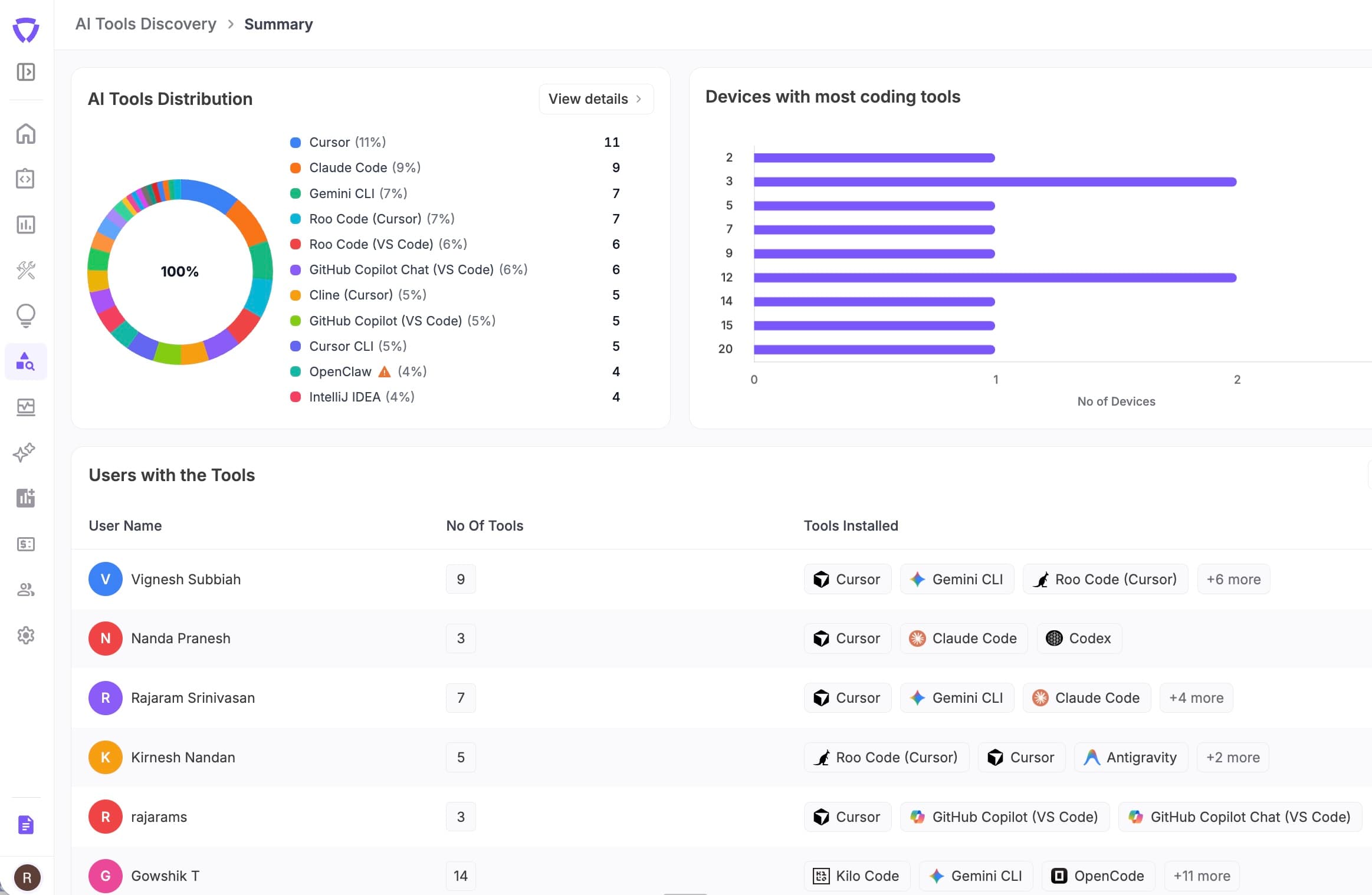
Complete agent inventory in minutes
Scan your entire engineering org to find every AI coding agent, MCP server, and tool integration. Know exactly what's installed, who's using it, and what permissions it has.
- ✓Detect Claude Code, Cursor, Windsurf, GitHub Copilot, Cline
- ✓Enumerate MCP servers and their configurations
- ✓Map IDE plugins across VS Code and JetBrains
- ✓Track installation drift over time
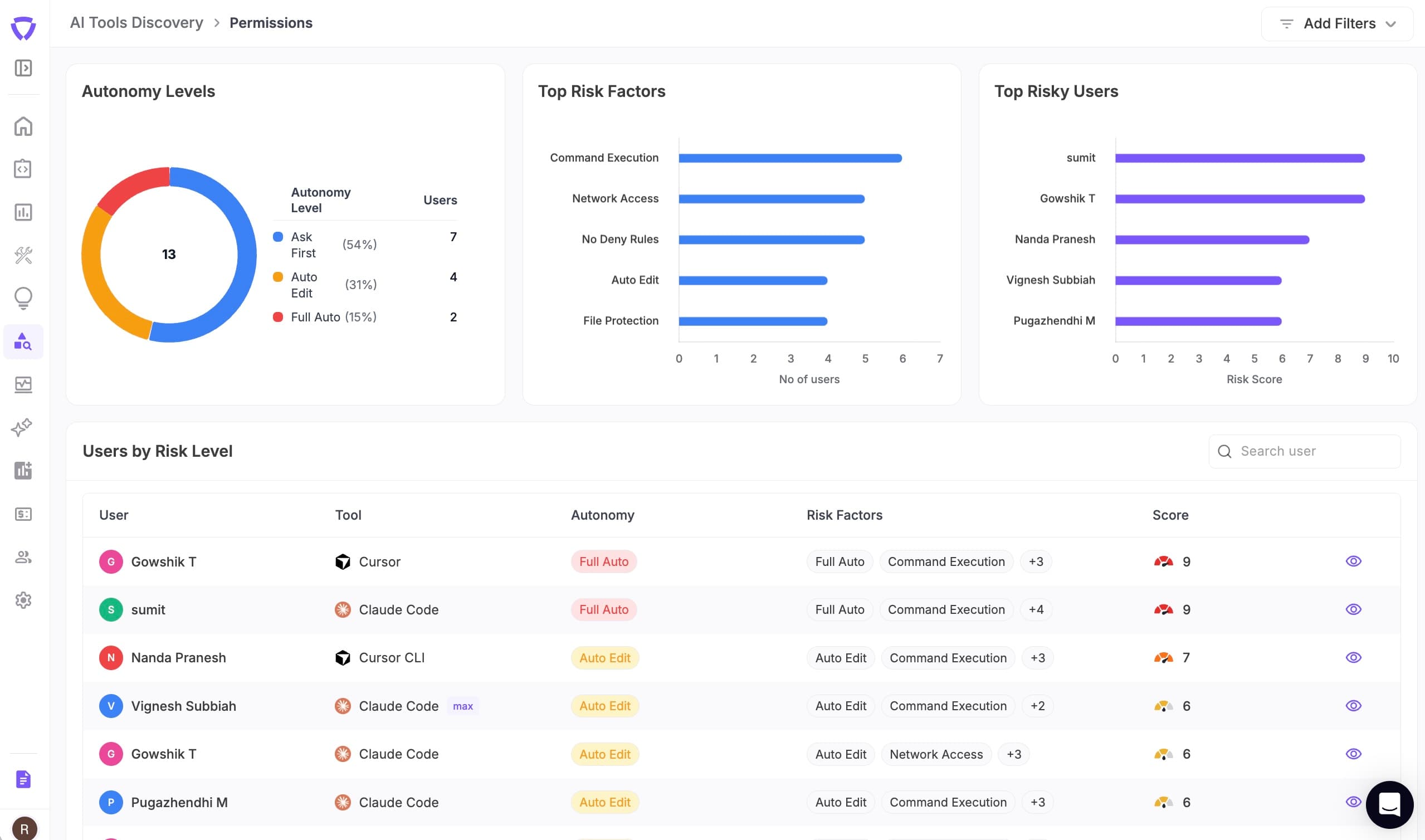
Surface risk before it becomes an incident
Score every developer's agent setup against security benchmarks. Surface misconfigurations, risky autonomy settings, and dangerous MCP connections.
- ✓Per-developer security posture scores
- ✓Risky MCP server connection alerts
- ✓Autonomy and permission risk analysis
- ✓Trend tracking and drift detection
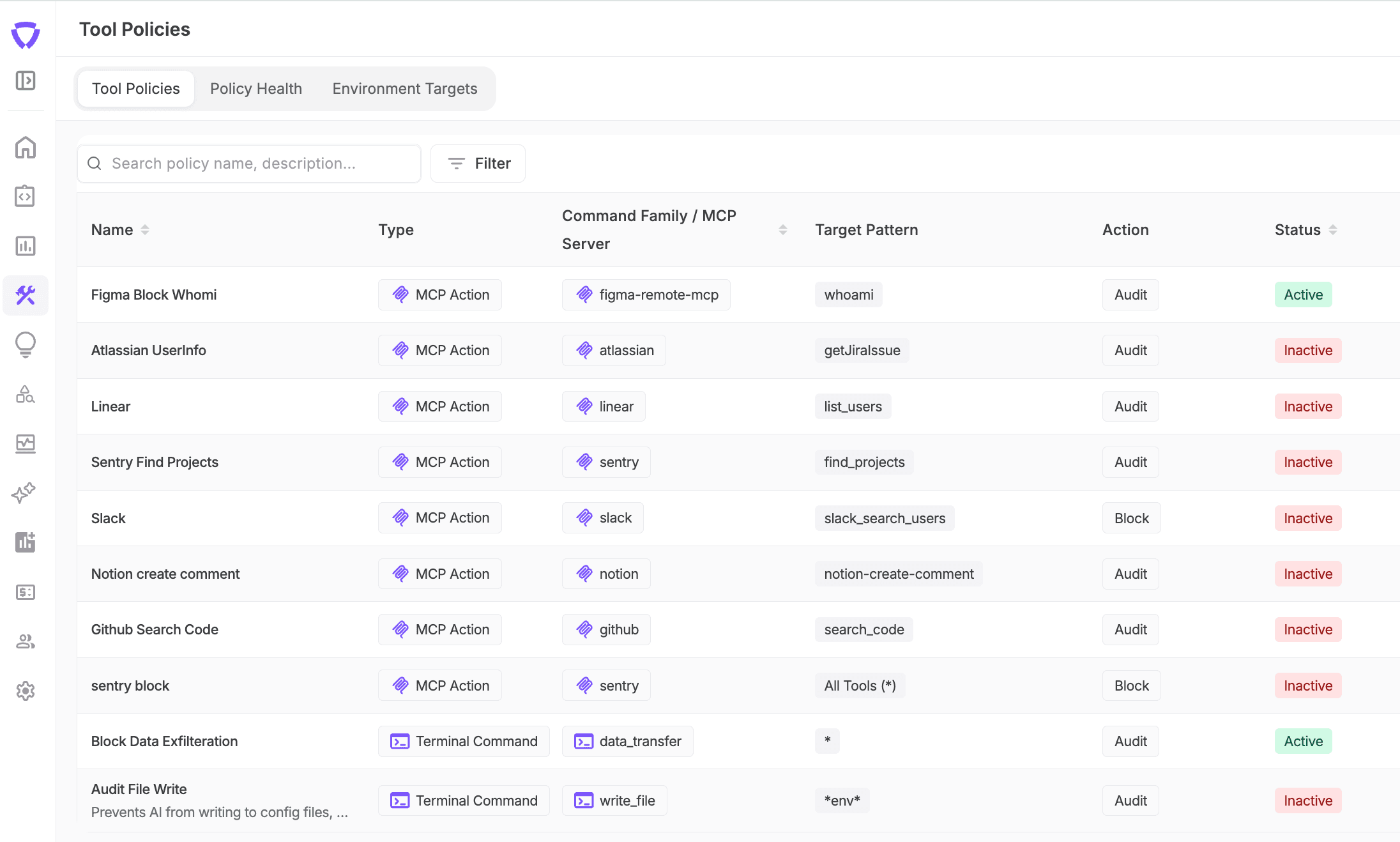
Enforce policy before damage is done
Define granular policies over what agents can and can't do. Audit, warn, block, or require human approval for sensitive operations.
- ✓Terminal command allow/deny with semantic parsing
- ✓MCP server connection and action policies
- ✓Approval workflows for high-risk operations
- ✓Full audit log of every agent action
Things we have seen AI coding agents do in the wild
These aren't hypothetical — these are real actions taken autonomously by AI coding tools, as seen by Unbound Gateway processing millions of tool use actions weekly.
Why existing controls aren't enough
Your security stack was built for humans using SaaS apps — not for autonomous agents running terminal commands and calling MCP servers.
| Existing Control | What It Does Well | What It Misses |
|---|---|---|
| AppSec / SAST | Finds code vulnerabilities after code is written | Doesn't guide live terminal commands or MCP invocations |
| IAM / PAM | Controls identity and access management | Doesn't understand agent autonomy or MCP servers |
| EDR / Endpoint | Sees process activity on endpoints | Can't explain agent intent or enforce session policy |
| AI Gateway | Routes and secures model API traffic | Misses IDE posture, terminal behavior, MCP actions |
| CASB / DLP | Governs SaaS access and data loss prevention | Not built for IDE/CLI workflows or approval logic |
A new control layer is needed — one built specifically for AI coding agent governance.
What security leaders are saying
“Unbound empowers THG Ingenuity teams to securely leverage frontier AI models within enterprise-grade controls. Its seamless open-source tool integrations streamlined developer onboarding, accelerating adoption of the latest advancements.”

Abraham Ingersoll
CISO, THG Ingenuity
“Unbound enables Exterro to uphold top-tier data security and global compliance standards while securely adopting AI. Teams consistently praise the intuitive platform that meets enterprise protocols and accelerates innovation.”

Anthony D
CISO, Exterro

Frequently asked questions
Common questions from security leaders evaluating Unbound.
Ready to govern your AI agents?
Get full visibility in under 5 minutes. No code changes, no developer disruption.